Scan Your Codebase for Critical Vulnerabilities in 2 Minutes
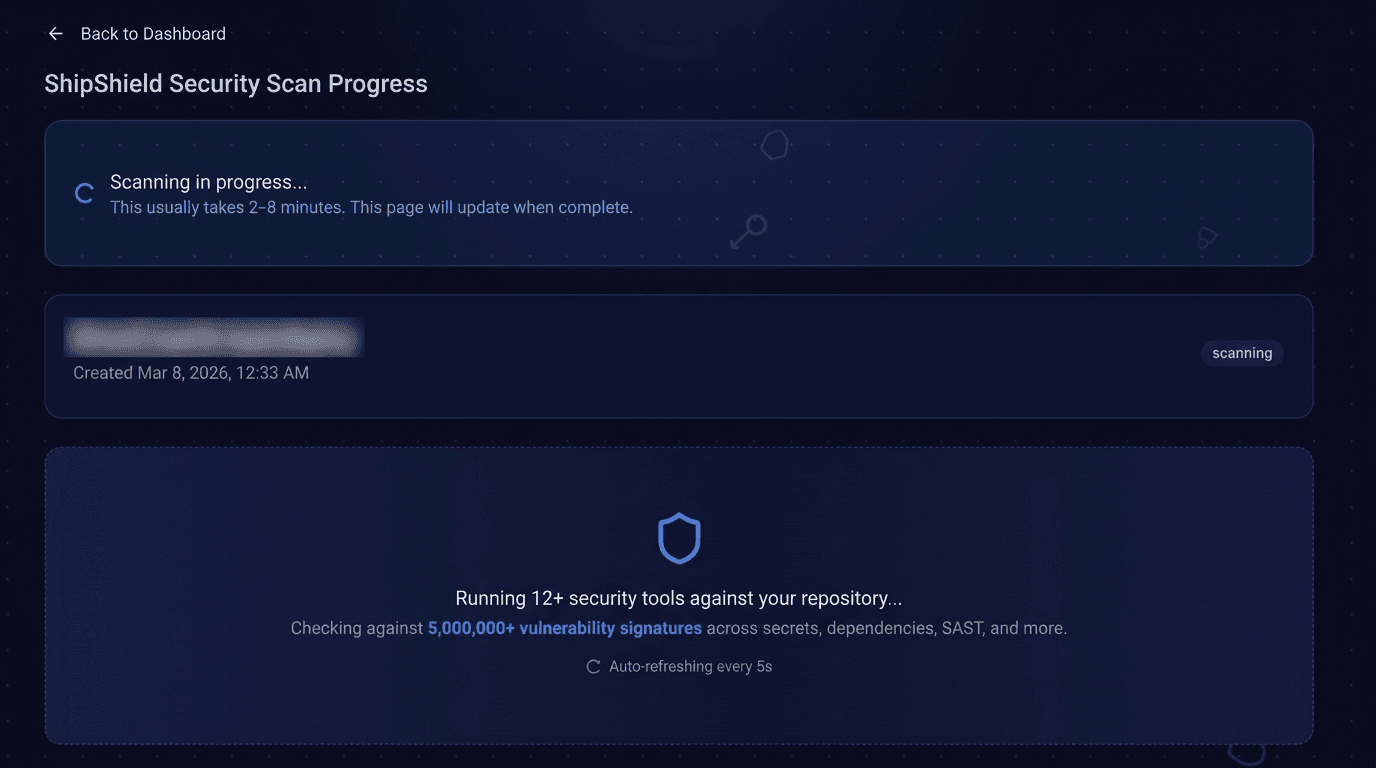
ShipShield's proprietary security engine checks your entire codebase against 5,000,000+ known vulnerability signatures and delivers a professional audit report with AI-powered fixes in minutes, not weeks.
5M+ vulnerability signatures · GitHub integration · $25 one-time scan
10,500+ Websites scanned with ShipShield
What We're Finding
Real data from 10,594 websites scanned by ShipShield.
68%
of sites have no security.txt found
58%
of sites have missing Permissions-Policy
52%
of sites have missing Content-Security-Policy (CSP)
49%
of sites have missing Referrer-Policy
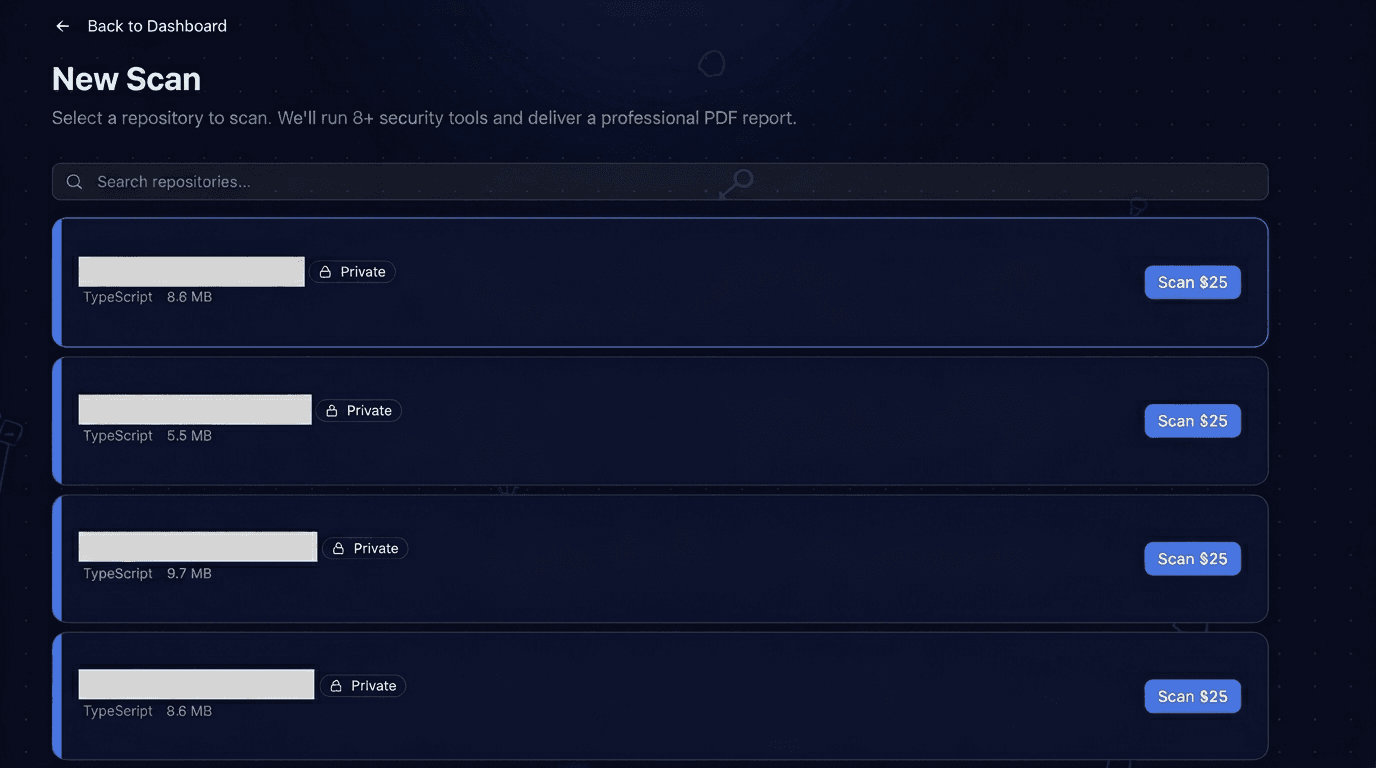
How It Works
Three steps to a secure codebase
14 Security Categories, One Engine
Our engine cross-references findings across every category to surface risks that single-point tools miss.
Exposed Secrets
API keys, credentials, and tokens in code and git history
Auth & Authorization
Missing auth checks, weak JWT config, privilege escalation
Injection Vulnerabilities
SQL injection, XSS, SSRF, command injection
Data Exposure
Sensitive data in client bundles, verbose errors, debug mode
Security Misconfiguration
CORS, missing headers, CSRF, default credentials
Dependency CVEs
Known vulnerabilities in npm, pip, cargo, and go packages
Business Logic
Input validation, race conditions, prompt injection vectors
Sensitive Data Flows
PII logging, unencrypted data transmission, storage issues
Infrastructure
Rate limiting, request size limits, file upload restrictions
Docker & IaC
Container misconfigs, exposed ports, running as root
License Compliance
GPL/AGPL copyleft detection across all dependencies
Software Bill of Materials
SPDX-format SBOM generation for compliance and audits
Supply Chain Security
Typosquatting detection and suspicious package analysis
Container Image Scanning
OS-level CVEs in Docker base images via Trivy
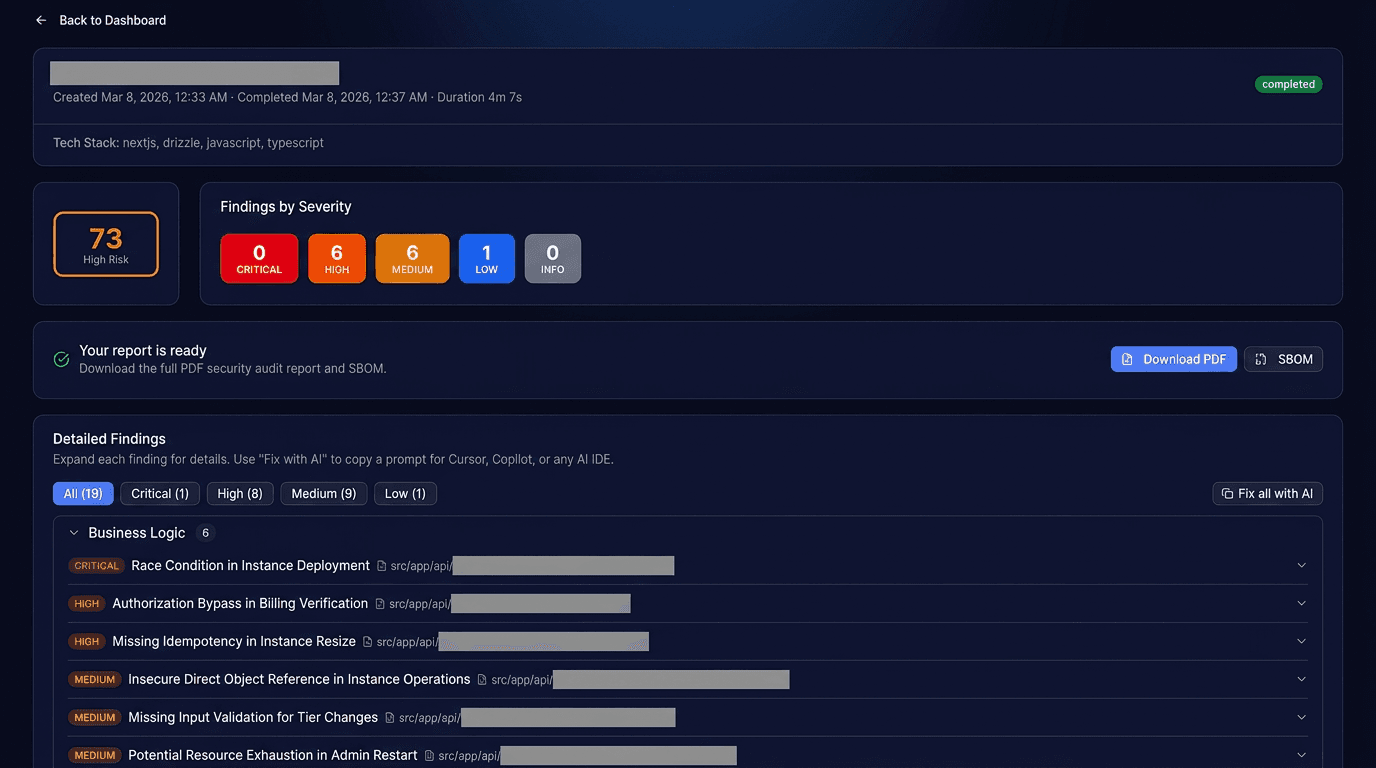
See What You Get
A professional security audit report, delivered in minutes.
SHIPSHIELD SECURITY AUDIT REPORT
Repository: your-org/your-repo
Risk Score
72/100 (Medium Risk)
[C-1] Stripe Secret Key Exposed
Severity: Critical · src/lib/stripe.ts:42
A Stripe secret key (sk_live_...) was detected in source code. Exposed API keys allow attackers to access your Stripe account and perform unauthorized transactions.
Quick Checks
- No SQL injection patterns found
- CORS misconfigured
- Missing CSRF protection
This Happens Every Day
Real incidents from companies and developers who shipped vulnerabilities.
Twitch
@Twitch
We can confirm a breach has taken place. Our teams are working with urgency to understand the extent of this.
125 GB of source code and creator payouts leaked
Oct 2021
CircleCI
@CircleCI
We want to make you aware of a security incident that occurred. Immediately rotate any and all secrets stored in CircleCI.
Attacker exfiltrated customer env vars, tokens, and keys
Jan 2023
Codecov
@codecov
We recently learned that someone had gained unauthorized access to our Bash Uploader script and modified it without our permission.
Compromised for 2 months before discovery, 29,000 customers affected
Apr 2021
GitHub
@GitHubSecurity
GitHub detected unauthorized access to npm production infrastructure using a compromised AWS API key, downloading private repos from dozens of orgs.
Stolen Heroku and Travis CI OAuth tokens used in attack
Apr 2022
The Register
@TheRegister
Developer stunned by $82,314 Gemini API key bill after theft. Researchers found 2,863 live Google API keys exposed that authenticate to Gemini.
46,000% spike in charges within 48 hours
Mar 2026
GitGuardian
@GitGuardian
12.8 million authentication secrets and keys were leaked on GitHub in 2023. 90% were still valid 5 days after exposure.
28% increase from 2022, only 2.6% revoked within one hour
Mar 2024
One Price. No Subscriptions.
Everything you need for a comprehensive security audit.
$25
- One-time scan
- No subscription
- Results in 2-8 minutes
- Refund if scan fails
Security Scanning
- 12+ security scanning tools
- Git history secret detection
- Live credential verification
- Dependency CVE scanning
- License compliance checking
- Supply chain & typosquatting detection
- Container image vulnerability scanning
Reports & Fixes
- Professional PDF report
- SBOM (Software Bill of Materials) export
- Fix suggestions with code examples
- AI IDE fix prompts (Cursor, Copilot, etc.)
- AI-powered business logic review
Experience
- GitHub integration (public & private repos)
- Email notification when ready
- No code stored after scan
No account needed to start. Pay once, scan once.
Not ready? Try a free website scan first →From the Blog
Security insights and best practices for shipping secure code.
The Security Headers Every Website Needs (And Why Most Are Missing Them)
Most websites ship without basic security headers, leaving them vulnerable to clickjacking, XSS, and data leaks. Here's what you need and how to add them.
The $25 Security Audit That Scored Our Codebase 78 Out of 100
We ran ShipShield on a real codebase. It found 1 critical vulnerability, 1 high severity issue, and 3 medium findings in under two minutes.
4,660 Websites, 34,793 Findings: The State of Web Security in 2026
We analyzed security data from over 4,600 websites. Half of all findings are missing security headers, 94% lack a security.txt, and the average risk score is 45 out of 100.
Frequently Asked Questions
Ship With Confidence
Get a professional security audit for your codebase in minutes.
Start Your Security Audit