We Scanned 100 Startup Websites. Here's What We Found.
We pointed ShipShield's free security scanner at 100 real startup websites. No cherry picking, no rigged sample. Just the first 100 companies from a public startup directory, scanned in under 60 seconds each.
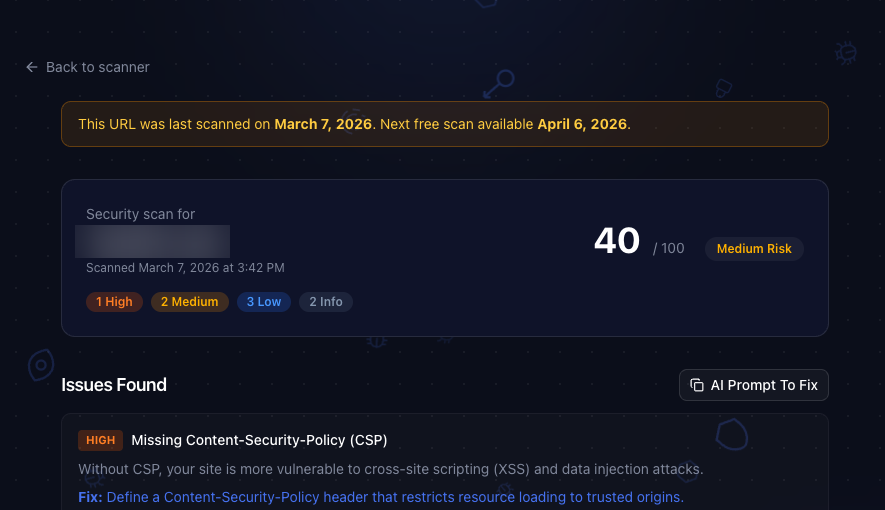
The average risk score? 45 out of 100. And that's just what's visible from the outside.
The Setup
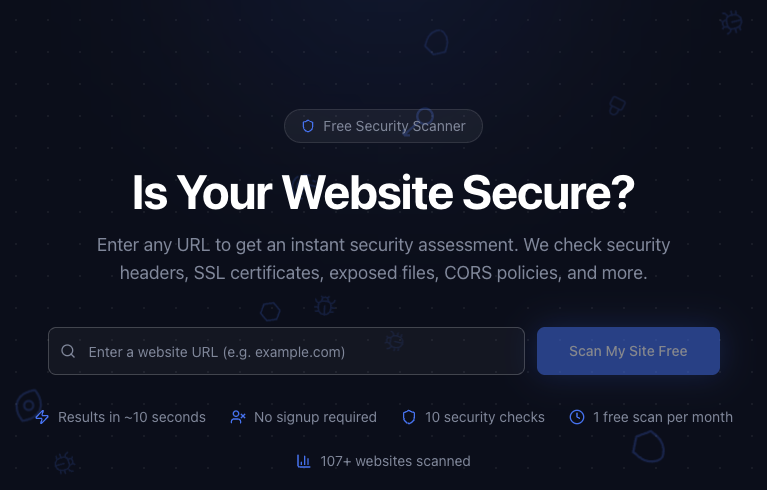
We used ShipShield's free scanner, the same one anyone can use at shipshield.ai/scan. It checks 10 things: security headers, SSL certificates, cookie security, exposed files, CORS policies, DNS records, technology fingerprinting, mixed content, redirect chains, and server information leakage.
No source code access. No authentication. Just what's publicly visible. If our scanner can find it, so can anyone else.
The Headline Numbers
Out of 100 startups:
- 80 had at least one high severity finding
- 96 had at least one medium severity finding
- 4 had critical issues (exposed sensitive files, dangerous misconfigurations)
- Only 13 scored below 25 on our risk scale
If your startup is in the "we'll deal with security later" phase, there's a good chance you're in the 87% that already has visible issues.
The Most Common Findings
Here's where it gets interesting. These aren't obscure edge cases. These are basic security hygiene items that most startups are shipping without.
Missing Security Headers
This was the biggest category by far. 94 out of 100 sites were missing at least one important security header.
Permissions-Policy83% missingReferrer-Policy76% missingContent-Security-Policy73% missingX-Frame-Options64% missingX-Content-Type-Options55% missingStrict-Transport-Security28% missing
The good news: every one of these can be fixed in about five minutes. (We wrote a whole guide on security headers if you want to know exactly what each one does.)
The bad news: most teams don't know they're missing them until someone checks.
DNS and Email Security
- 41% had no DMARC record
- 38% had no SPF record
Without these, anyone can send emails pretending to be your domain. Not great when you're asking customers to trust you with their data.
CORS Misconfiguration
29% of sites had Access-Control-Allow-Origin: * in their responses. That's basically telling every website on the internet "sure, make requests to our API, we don't mind." Sometimes that's intentional. Usually it's not.
Server Information Leakage
25% were exposing their backend technology through X-Powered-By or Server headers. Telling attackers you're running Next.js 14.2 or Apache 2.4.51 makes their job easier. Remove the header, remove the advantage.
The Risk Distribution
We score every scan from 0 (perfect) to 100 (we need to talk).
- 0 to 25 (Low Risk): 13 sites
- 26 to 50 (Medium Risk): 50 sites
- 51 to 75 (High Risk): 31 sites
- 76 to 100 (Critical Risk): 6 sites
Half of all startups landed in the 26 to 50 range. That's the "not catastrophic but definitely fixable" zone. The kind of stuff that takes a couple of hours to clean up but might never get prioritized until something goes wrong.
What Surprised Us
The best scoring sites weren't always the biggest. Some tiny, early stage startups had perfect scores. They clearly had someone on the team who cared about security from day one.
WordPress sites consistently scored worse. Not because WordPress is inherently insecure, but because the default configuration ships without most security headers, and plugins often introduce CORS and cookie issues.
Almost nobody had a security.txt file. 99 out of 100 sites were missing it. It's a simple text file that tells security researchers how to report vulnerabilities to you. Takes 30 seconds to add, and it could save you from a public disclosure instead of a private email.
What This Means For You
If you're building a startup, here's the uncomfortable truth: your website is probably in this dataset's majority. Not because you're bad at security, but because these things are easy to miss when you're focused on shipping features.
The fix is simpler than you think:
- [ ] Add the six essential security headers (see our header guide)
- [ ] Set up SPF and DMARC records for your domain
- [ ] Remove
X-Powered-Byheaders from your responses - [ ] Add a
security.txtfile to/.well-known/ - [ ] Check your CORS configuration (do you really need
*?)
But That's Just the Surface
Everything we checked in this study was publicly visible. We didn't look at source code, dependencies, secrets in git history, or infrastructure configuration.
When we run full codebase audits, we regularly find leaked API keys, outdated dependencies with known CVEs, SQL injection risks, and misconfigured auth. The kind of stuff that doesn't show up in a header check but could ruin your week.
73% of security vulnerabilities hide in source code and dependencies. A surface scan can only tell you what's visible from the outside.
Want to see where your site stands? Run a free scan. It takes about 10 seconds, no signup required.
If the results make you nervous, the full codebase audit covers everything else. It connects to your GitHub repo and scans 5,000+ vulnerability patterns across your entire stack. Four minutes, $25, and you'll know exactly where you stand.
Ship secure. Ship confident.
Secure Your Codebase
ShipShield scans your entire codebase for vulnerabilities, misconfigurations, leaked secrets, and outdated dependencies. Get a full security audit in minutes.